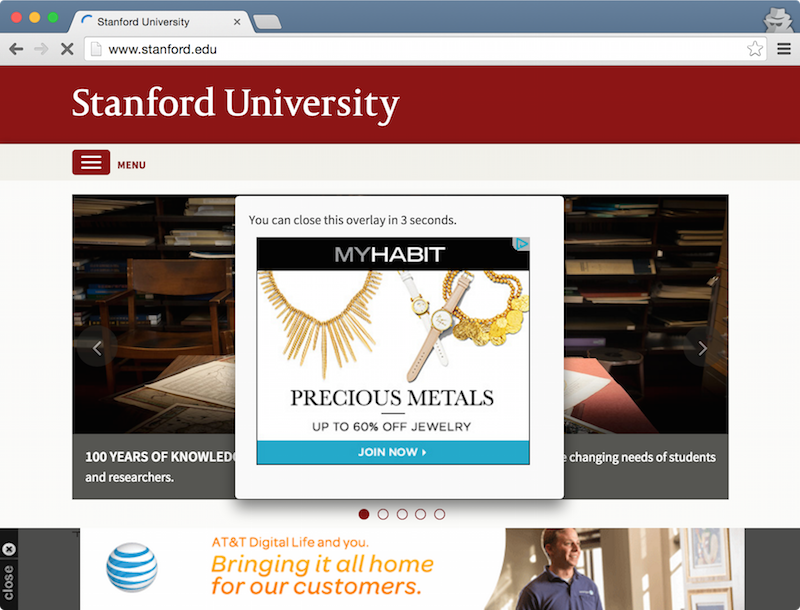
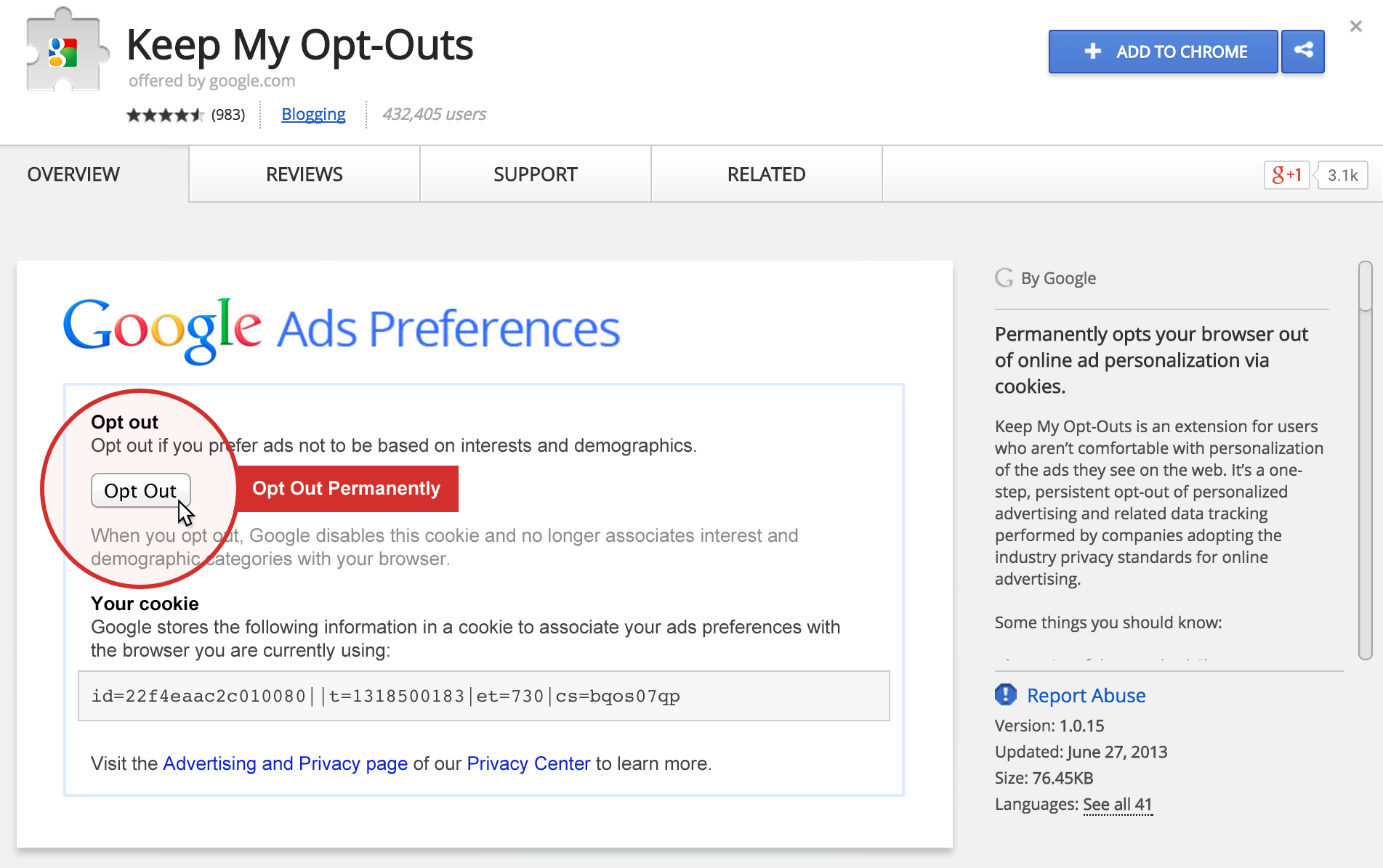
Over four years ago, Google launched a Chrome privacy extension. Keep My Opt-Outs arrived with a media splash, and it presently has over 400,000 users worldwide.1
It’s a top result on the Chrome Web Store,2 and it’s even endorsed by a faux celebrity.
Unfortunately, the Keep My Opt-Outs extension isn’t nearly as effective as Google claims. It hasn’t been updated for years, resulting in only half of the promised coverage. Keep My Opt-Outs also doesn’t work in Chrome’s private browsing mode, despite the user’s explicit permission.
If you’re currently running Keep My Opt-Outs, I’d encourage switching to Disconnect or Privacy Badger.3 Adblock, Adblock Plus, and Ghostery are also excellent privacy tools, when configured properly.
In this post, I’ll explain why Google emphasized the Keep My Opt-Outs extension, how the code works, and what went awry.
… →